LaSorsa & Associates is an international provider of Technical Surveillance Counter Measures, Bug Sweeps & Counter Surveillance to detect and eradicate electronic eavesdropping devices or “Bugs” for clients that require discreet counter- surveillance solutions. We utilize modern, state-of-the-art and professional equipment in order to perform sweeps to identify various types of audio and video interception devices.
Bug Sweeps – Eavesdropping Detection – Technical Surveillance Counter Measures (TSCM)
Exposures and uncertainty diminish your sense of security in the places
where you should feel most secure.
RESTORE YOUR SENSE OF SECURITY
For more information or to explain your situation so we can recommend which course of action would be best for you.
You can call us at 888-831-0809 or email us at INFO@LASORSA.COM
You can also fill out the form to the right.
–
What is your peace of mind worth?
–

–
What is your information worth to you? …To your competition?
–
 See our Brochure
See our Brochure
–
We utilize state-of-the-art devices to perform frequency spectrum analysis and other technical searches. These search techniques cover the entire usable frequency spectrum and can even find bugs that are inactive or turned off. In addition, the area will be physically inspected thoroughly to detect covert devices. Our technicians are some of the most highly trained specialists in the world, most with former federal agency training and experience.
–
Counter Surveillance
The correct TSCM tools and properly trained personnel can help with the following:
- TSCM Services & Bug Sweeps
- Corporate Counter-Espionage
- Residential & Domestic Issues
- Wiretap & Bug Detection
- Counter-Surveillance
- Electronic Surveillance Detection
- Covert Video Device Detection
- Audio Recording or Transmitting Devices
- Vehicle Tracking Devices – GPS
- Listening Device Detection
- Hidden Camera Detection
–
TSCM Bug Sweep
TSCM / Bug Sweeps are usually conducted because of the following:
- Suspicion that business or personal conversations are being intercepted.
- Suspicion of the existence of a listening device.
- Noise on the telephone lines.
- Unsolicited telephone repairman visits.
- Information leaks.
- Evidence left behind by burglars/intruders.
- Domestic or business problems.
–
–
–
TSCM
TSCM Equipment We Use:
Frequency Spectrum Analyzer
Ultra-Sensitive VLF/UHF/IR Probe
Field Strength Meter
Telephone Line Analyzer
Wireless Camera/Video Receiver/Interceptor
GSM (Cell Phone), Wi-Fi & Bluetooth Detector
IR/Thermal Imagery Equipment
Non-Linear Junction Detector/Evaluator
Network Protocol Analyzer
Black Light/UV Light Inspection Equipment
Multi-Meter & Outlet Tester
Borescope & Other Physical Inspection Tools
–
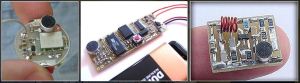
Devices like these could be ruining your business or your personal life.
Let us restore your sense of security.
–
Initial consultations are always free, discreet and personal.
We provide these services in the following areas:
California Colorado Florida Georgia Hawaii Maryland New Jersey
New York North Carolina Ohio South Carolina Texas
Call 888-831-0809 or email info@lasorsa.com
–
–